Configurations
The following standard configurations are currently available.
In addition to the functionality described, each also implements layer 3/4 & 7 DDoS protection in a transparent fashion.
1. Static: Static Content Site
Description
This configuration is intended to provide a reasonable balance between cache performance, and the need for site administrators to ensure content updates are available reasonably quickly.
Important: This configuration assumes the site does not require any server-side session functionality in order to function as intended (e.g. Session cookies)
Cache duration
This configuration will cache all UI related images, fonts and video content for *5 minutes *. This includes resources with the following extensions:
All other resources (e.g. actual pages) will also be cached for 5 minutes
2. Session: Session-based Site / Web Application
Description
This configuration is intended to provide a 'safe' configuration for a site / web application that depend on session-based information to function as intended (e.g an ASP.NET application with a login, and JSP application with a login, an application that depends on session affinity). In general, UI related aspects are cached for a longer duration, while pages etc. are not cached.
Cache duration
This configuration will cache all ui related images, fonts and video content for 5 minutes. This includes resources with the following extensions:
All other resources (e.g. actual pages) will NOT be cached. All requests that fall into this category will always be forwarded to the origin server, complete with any headers (including cookie values) that were included with the request.
3. Transparent: No caching.
Description
This configuration is intended as a safe deployment option for any site or application. No requests are cached. ALL requests are ALWAYS forwarded to the origin. The integrity of the original request is respected, with no removal of headers, cookie values or querystring params. All HTTP verbs are permitted.
Cache duration
This configuration provides NO caching.
Notes
- All configurations use TLS v1.1 as a minimum for connections to the origin (where HTTPS/TLS is used).
- CloudFront currently has TLS 1.0 enabled. It is not possible to disable this. This does not equate to weak TLS or weak ciphers.
- HTTP/2 is enabled by default.
- Full logging is enabled (including cookie logging).
- The results of HTTP POST requests are NOT cached - regardless of the cache behavior configuration.
- the Authorization header is automatically passed to the origin. This ensures these configurations are 'safe' for sites using header-based Authentication tokens.
- CloudFront's own geo-location header: CloudFront-Viewer-Country will be added to origin requests to provide geo-location data to the origin.
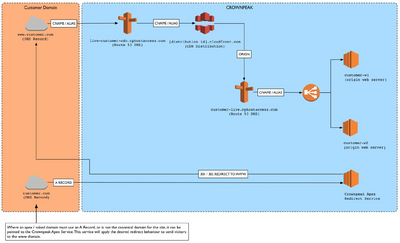
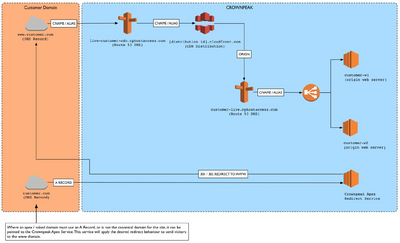
DNS Architecture
The following diagram represents the standard DNS architecture for CloudFront deployments, as of December 2016. Expect legacy CloudFront deployments to have a range of (sometimes bewildering) approaches to DNS configuration. Dig / nslookup is your friend.